SECURING PHYSICAL AND VIRTUAL SITES
Sensitive residences and private life
Vip offices
Sensitive buildings or industrial sites
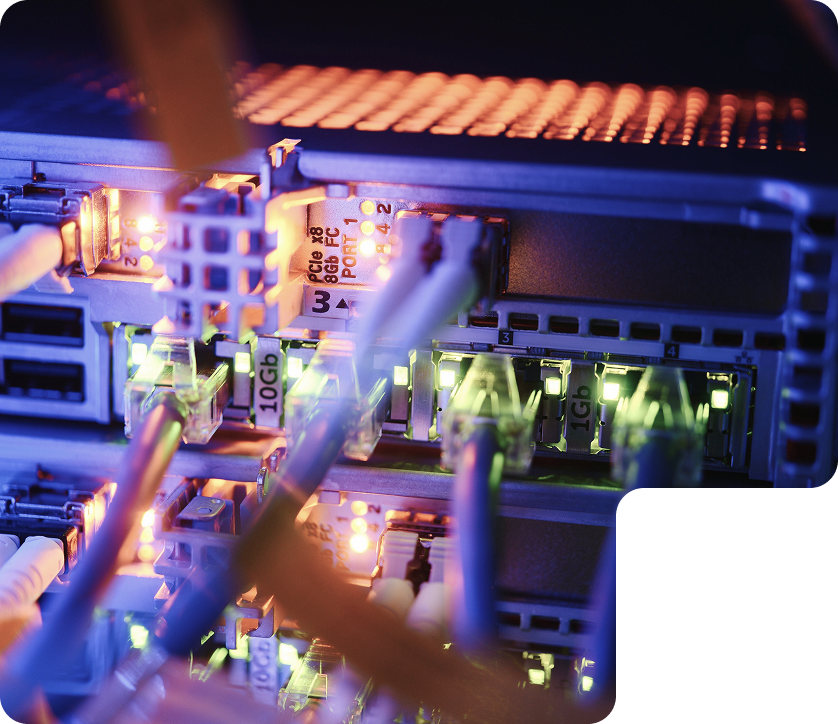
Networks for sensitive residences,
VIP offices and
strategic industrial sites


Networks at sensitive sites, whether private residences, VIP offices or strategic industrial sites, must guarantee impeccable security due to the critical nature of the exchanges taking place there.
Thanks to a technological partnership with a leading equipment manufacturer, we design “safe sites” based on wired and wireless networks that are secure from the outset (by design). The artificial intelligence (AI) built into our solutions automatically detects, geolocates and categorizes all connected devices, while reporting any anomalies to our Center of Expertise, which ensures continuous, proactive monitoring.

Infrastructure design and safety

The Expertise Center designs network architectures adapted to the specific risks associated with the activity or geographical location of the sites. These infrastructures are designed to withstand the main threats:
Intrusions : Block unauthorized access and proactively detect penetration attempts.
Eavesdropping: Systematic encryption of communications to prevent interception of sensitive data.
Terminal spyware: Protection against spyware or insecure devices that could compromise the network.
Exfiltration of sensitive data: Neutralize data theft attempts with rapid detection and response mechanisms.

In addition to design, our experts oversee the supply of equipment via a strictly controlled supply chain, eliminating any risk of manipulation or alteration by unauthorized third parties.
Building safety from
the design stage

Integration and proactive monitoring


We ensure the complete integration of network infrastructures, following rigorous processes that guarantee their robustness from the moment they are commissioned. Continuous monitoring is carried out via our Security Operations Center (SOC), with enhanced use of artificial intelligence (AI), which enables :

Automatically detect intrusions and anomalies: Thanks to AI, our systems identify unusual or unauthorized behavior in real time, detecting infected or compromised devices.

Automatically block threats: AI-based solutions immediately neutralize suspicious connections and isolate compromised machines to prevent their spread.

Anticipate emerging vulnerabilities: AI continuously analyzes events to identify and address risks before they are exploited.

React quickly to incidents: If a threat is detected, automated responses are triggered, supplemented by human intervention if necessary, to neutralize risks with maximum efficiency.
AI guarantees proactive and dynamic monitoring, capable of responding to the most sophisticated cyber-attacks, while reducing reaction times and strengthening the overall resilience of infrastructures.
By combining rigorous design, cutting-edge technologies and AI-based solutions, we offer secure networks tailored to the needs of the most sensitive sites, guaranteeing the protection of critical infrastructures and the peace of mind of their occupants.





Contact
We are here to listen to you
Need support or a tailored solution? Our team is here to answer all your questions. We’re here to listen.


 Linkedin
Linkedin